With single devices or small networks, it can be easy to set up additional devices, but this piecemeal approach can be dangerous as businesses grow. Over time, file integrity can be compromised and IT becomes unreliable, resulting in a negative impact on business performance and productivity. Relying on external help, users often don’t understand the core issues and don’t know what is being done to fix problems, or the longer-term impact. This leads to the external IT team being perceived as a necessary (and often expensive) cost, without really understanding why, or knowing if they are providing value for money.
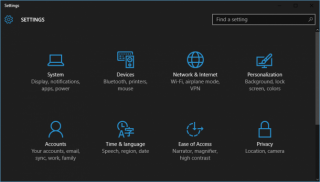
We believe that IT should be seen as a simple utility like water and electricity – inherently reliable and always ON, with added flexibility to grow and adapt as organisations change. At Bongo IT, we offer a set of core services through a simple menu-based approach, such as broadband, email, telephony and general IT support to name a few. We audit current requirements and provide a comprehensive IT Strategy Review, ensuring that customers clearly understand their requirements now and into the future, and only pay for the services they need.